Buy used Reference books online in India
Buy Second Hand Books, Used Books Online In India
Oxford English-English-Hindi Dictionary
This is the revised edition of our consistent bestseller, the English-English-Hindi Dictionary edited by Dr Suresh Kumar and Dr Ramanath Sahai contains more than 52,000 entries, related phrases, idioms and more than 200 illustrations. Like our other Bilingual Dictionaries, this has beenspecially compiled for learners of English, teachers, translators and general readers. English-English-Hindi Dictionary companion DVD The print dictionary also has a companion DVD with the following features: * A search option that can be used to search through the entire wordlist of the dictionary.* Each of the headwords and derivatives in the dictionary has an audio for pronunciation guide which the user can listen to by clicking on an icon.* The user can also type in Hindi to search through the Hindi part of the dictionary.
JavaScript: The Definitive Guide
For web developers and other programmers interested in using JavaScript, this bestselling book provides the most comprehensive JavaScript reference section on the market. The seventh edition represents a significant update, with new material for ECMAScript 2017 (ES8), and new chapters on language-specific features.JavaScript: The Definitive Guide is ideal for experienced programmers who want to learn the programming language of the web, and for current JavaScript programmers who want to master it.
Pocket Merriam-Webster Dictionary By Langenscheidt
This modern monolingual dictionary contains today's essential vocabulary in a compact and handy format. This makes it ideal for expanding your vocabulary, improving your understanding of English and perfecting your communicative abilities. Clear and concise definitions of the meanings of the most commonly used words in the English language Pronunciation of all main headwords Fully syllabification Brief etymologies Useful appendices with Foreign Words and Phrases, Nations of the World, Population figures of the United States and Canada, and Signs and Symbols.
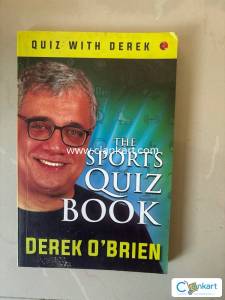
THE SPORTS QUIZ BOOK
Who named Milkha Singh, who won India’s first Commonwealth gold, ‘The Flying Sikh’? Accordingto Usain Bolt, what inspired him to come up with his famous ‘To Di World’ victory pose? The2010 film Invictus revolves around which sport? Which footballer was described as ‘Pythagoras inboots’ for the complexity and precision of his angled passes?Find the answers to these and many more in The Sports Quiz Book. In these pages, Derek O’Brienbrings together an astonishing range of questions in categories that include Athletics, Badminton,Board Games, Boxing, Card Games, Entertainment and Sports, Formula 1, Fifa World Cup, IndianPremier League, Olympic Games, Tennis, Cricket—to name just a few. Also to be found afterevery chapter are fun, unusual facts and trivia about sports and a compilation of some of the bestand most inspiring quotations by sportspersons.So whether you are a quiz buff, a sports maniac or just want to brush up your knowledge aboutevery aspect of sports, The Sports Quiz Book is what you need to catch up on!
CISSP EXAM GUIDE 8TH EDITION BY SHON HARRIS
A new edition of Shon Harris' bestselling exam prep guide--fully updated for the new CISSP 2018 Common Body of KnowledgeThis effective self-study guide fully prepares you for the challenging CISSP exam and offers 100% coverage of all exam domains. This edition has been thoroughly revised to cover the new CISSP 2018 Common Body of Knowledge, hot spot and drag and drop question formats, and more.CISSP All-in-One Exam Guide, Eighth Edition features hands-on exercises as well as "Notes," "Tips," and "Cautions" that provide real-world insight and call out potentially harmful situations. Each chapter features learning objectives, exam tips, and practice questions with in-depth answer explanations. Beyond exam prep, the guide also serves as an ideal on-the-job reference for IT security professionals.-Fully updated to cover 2018 exam objectives and question formats-Digital content includes access to the Total Tester test engine with 1500 practice questions, and flashcards-Serves as an essential on-the-job-reference
OPERATING SYSTEM CONCEPTS - NINTH EDITION
The tenth edition of has been revised to keep it fresh and up-to-date with contemporary examples of how operating systems function, as well as enhanced interactive elements to improve learning and the student�s experience with the material. It combines instruction on concepts with real-world applications so that students can understand the practical usage of the content. End-of-chapter problems, exercises, review questions, and programming exercises help to further reinforce important concepts. New interactive self-assessment problems are provided throughout the text to help students monitor their level of understanding and progress. A Linux virtual machine (including C and Java source code and development tools) allows students to complete programming exercises that help them engage further with the material.
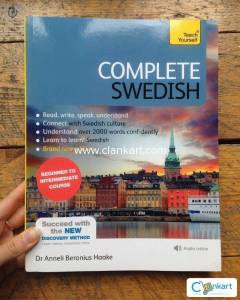
Complete Swedish
Do you want to develop a solid understanding of Swedish and communicate confidently with others?Through authentic conversations, vocabulary building, grammar explanations and extensive practice and review, Complete Swedish will equip you with the skills you need to use Swedish in a variety of settings and situations, developing your cultural awareness along the way.What will I achieve by the end of the course?By the end of Complete Swedish you will have a solid intermediate-level grounding in the four key skills - reading, writing, speaking and listening - and be able to communicate with confidence and accuracy.Is this course for me?If you want to move confidently from beginner to intermediate level, this is the course for you. It's perfect for the self-study learner, with a one-to-one tutor, or for the beginner classroom. It can also be used as a refresher course.What do I get?-18 learning units plus verbs reference and word glossary and revision section-Discovery Method - figure out rules and patterns to make the language stick-Teaches the key skills - reading, writing, listening, and speaking-Learn to learn - tips and skills on how to be a better language learner-Culture notes - learn about the people and places of Sweden-Outcomes-based learning - focus your studies with clear aims-Authentic listening activities - everyday conversations give you a flavour of real spoken Swedish-Test Yourself - see and track your own progress*Complete Swedish maps from Novice Low to Advanced Low level proficiency of ACTFL (American Council on the Teaching of Foreign Languages) and from A1 Beginner to B1/B2 Upper Intermediate level of the CEFR (Common European Framework of Reference for Languages) guidelines.The audio for this course can be downloaded from the Teach Yourself Library app or streamed at library.teachyourself.com.
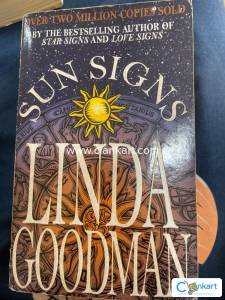
Sun Signs by Linda Goodman
Find out what's really happening in your life and the lives of those around you. Is he really unstable beneath that placid exterior? Is she marrying you for your money alone? When should you give a wayward spouse the benefit of the doubt? How can you adjust your inner moods to your best advantage, knowing when to push and when to pull back, when to speak up and when to shut up? What is the best time to ask your boss for that raise, your girl for her heart and hand, your brother-in-law for a loan? Learn all this and much, much more from the world-famous astrologer who has helped millions divine their way to happiness, love, and profit by studying the sun signs. Amaze your friends and yourself with your insight into their most hidden characteristics. Be the best that you can possibly be with -- Sun Signs.
CCNA Routing and Switching Second Edition Todd Lammle
According to DOEACC M4.1-R3 Syllabus effective from July, 2003 Examination,This book covers the entire syllabus for Module 4.1-R3 paper namely, Programming and Problem Solving through 'C' Language, in clear and simple style. Each concept in the book is illustrated with practical examples. The book elucidates both basic and advanced topics in 'C'.This book also presents a detailed discussion on arrays, pointers and functions in a manner that students of science, art or commerce streams can understand these topics very easily.Special Features of the book are:Steps in program development are explained in easy to understand language.Programming basics such as how to use different types of controls, functions, pointers, data structures and unions are clearly presented with suitable examples.A set of review questions with answers added at the end of each chapter. Inclusion of a set of sample papers help readers to well prepare themselves before appearing for the DOEACC examination.A comprehensive index and glossary of technical terms are added for easy access and thorough understanding of the subject matter.
The complete reference c++ fourth edition
Best-selling genius Herb Schildt covers everything from keywords, syntax, and libraries, to advanced features such as overloading, inheritance, virtual functions, namespaces, templates, and RTTI?plus, a complete description of the Standard Template Library (STL). About The Author Herbert Schildt is a world leading programming author. He is an authority on the C, C++, Java, and C# programming languages, and a master Windows programmer. His programming books have sold more than three million copies worldwide and have been translated into all major foreign languages. He is the author of numerous best sellers including C: The Complete Reference, Java 2: The Complete Reference, Java 2: A Beginner's Guide, C#: A Beginner's Guide, and many more. Schildt holds a master's degree in computer science from the University of Illinois. Table Of Contents Part I: The Foundation of C++: The C Subset Part I: The Foundation of C++: The C Subset 1: An Overview of C 2: Expressions 3: Statements 4: Arrays and Null-Terminated Strings 5: Pointers 6: Functions 8: C-Style Console I/O 9: File I/O 10: The Preprocessor and Comments Part II: C++ 11: An Overview of C++ 12: Classes and Objects 13: Arrays, Pointers, References, and the Dynamic Allocation Operators 14: Function Overloading, Copy Constructors, and Default Arguments 15: Operator Overloading 16: Inheritance 17: Virtual Functions and Polymorphism 18: Templates 19: Exception Handling 20: The C++ I/O System Basics 21: C+
Muslim Astrologer Black Magic Love Problem
Error-correction coding is being used on an almost routine basis in most new communication systems. Not only is coding equipment being used to increase the energy efficiency of communication links, but coding ideas are also providing innovative solutions to many related communication problems. Among these are the elimination of intersymbol interference caused by filtering and multipath and the improved demodulation of certain frequency modulated signals by taking advantage of the "natural" coding provided by a continuous phase. Although several books and nu- merous articles have been written on coding theory, there are still noticeable deficiencies. First, the practical aspects of translating a specific decoding algorithm into actual hardware have been largely ignored. The information that is available is sketchy and is widely dispersed. Second, the information required to evaluate a particular technique under situations that are en- countered in practice is available for the most part only in private company reports. This book is aimed at correcting both of these problems. It is written for the design engineer who must build the coding and decoding equipment and for the communication system engineer who must incorporate this equipment into a system. It is also suitable as a senior-level or first-year graduate text for an introductory one-semester course in coding theory. The book U"Ses a minimum of mathematics and entirely avoids the classical theorem/proof approach that is often seen in coding texts.